In an increasingly data-conscious world, we recognise the utmost significance of data security and adherence to regulations. As a respected B2B SaaS website visitor identification software, our commitment lies in ensuring that your business flourishes within a secure and legally compliant setting.
At Dynamic Leads, our foundation is built on a strong dedication to safeguarding your data. We comprehend that shielding sensitive information is not only a priority but also a duty. For this reason, we've gone to great lengths to ensure that our lead management software seamlessly aligns with all pertinent data laws.
Our software is meticulously designed to adhere to a broad spectrum of data protection regulations, encompassing but not confined to the General Data Protection Regulation (GDPR), the California Consumer Privacy Act (CCPA), and any other sector-specific regulations that might pertain to your enterprise. We've painstakingly engineered our platform to incorporate privacy-by-design principles, ensuring that data protection is the cornerstone of our technology.
Here's how Dynamic Leads ensures compliance:
Data Encryption: We employ cutting-edge encryption techniques to uphold the confidentiality of your data. This ensures that any information conveyed or stored within our system remains encrypted and indecipherable to unauthorised parties.
User Consent Management: Our software empowers you to proficiently manage user consents. You possess the capability to transparently collect and document user consent, thereby ensuring your adherence to legal requisites for processing personal data.
Anonymisation and Pseudonymisation: We furnish features enabling you to pseudonymise or anonymise personal data as mandated by data protection laws. This grants you the ability to utilise the data while upholding compliance and respecting individuals' privacy.
Data Retention Policies: Dynamic Leads facilitates the establishment of automated data retention policies, guaranteeing data isn't retained longer than necessary and remains aligned with legal stipulations.
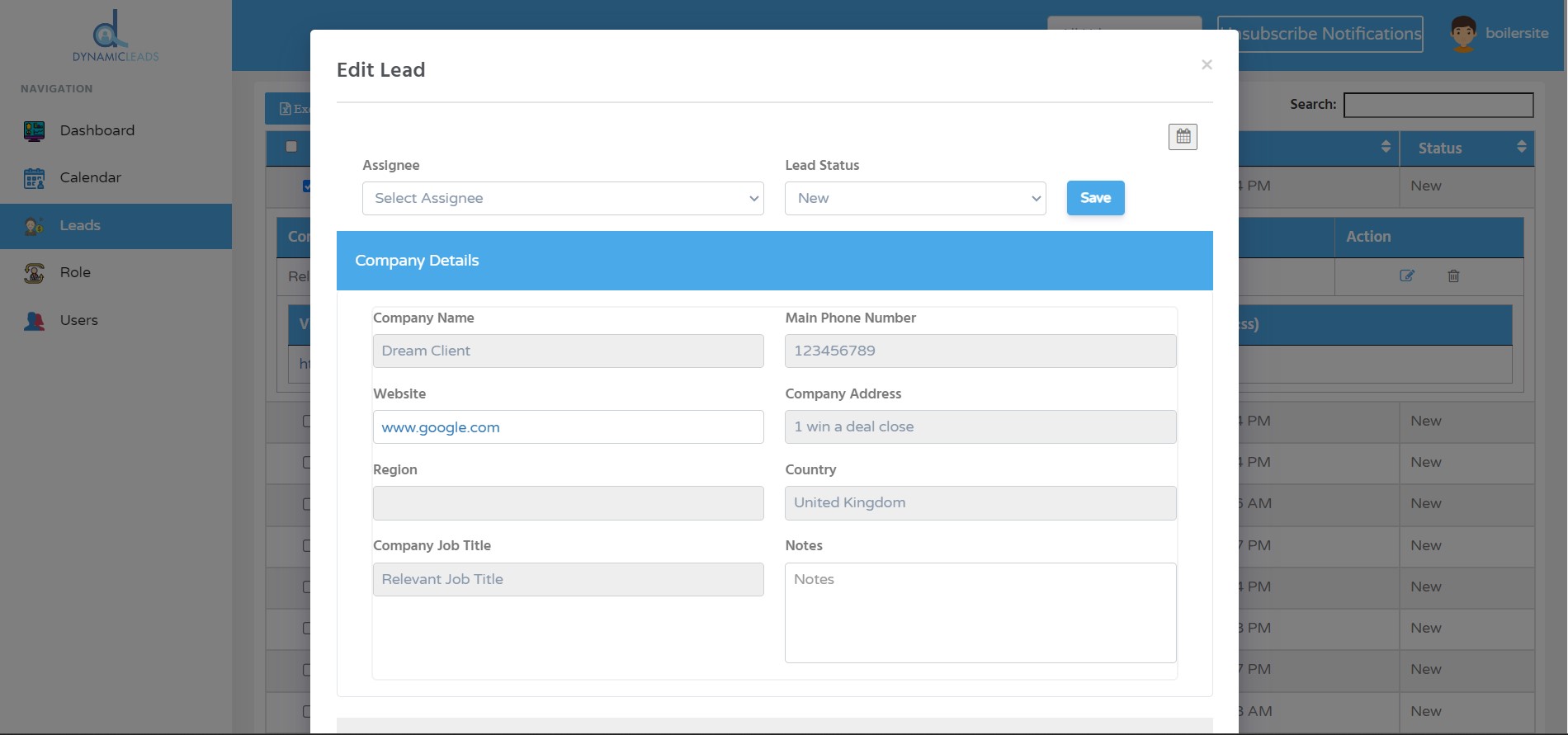
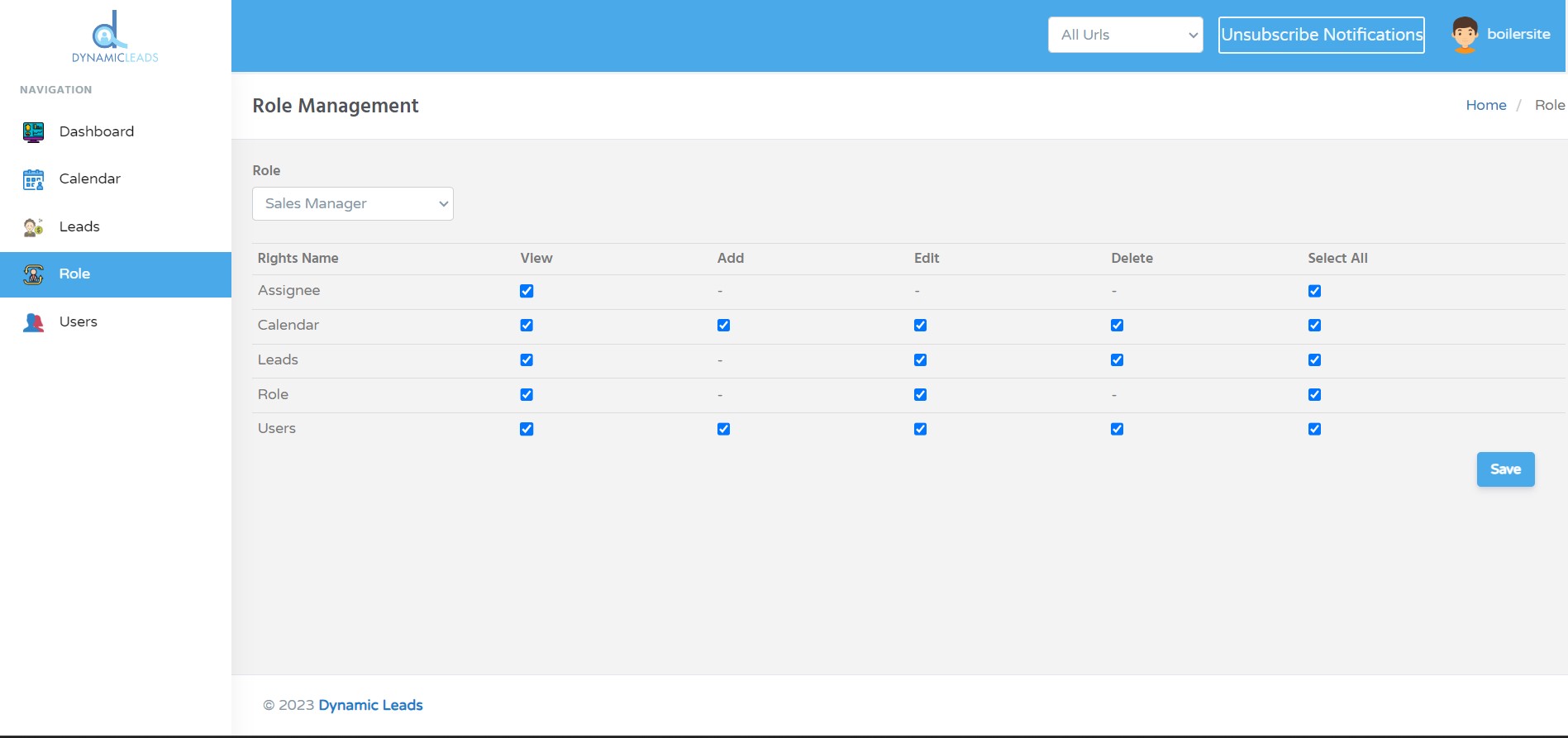
Data Access Controls: Stringent access controls are implemented, allowing only authorised personnel within your organisation to access sensitive data. This diminishes the risk of data breaches and unauthorised usage.
Regular Audits and Monitoring: Our dedication to compliance is a continual process. We regularly conduct audits and monitoring to recognise and rectify potential vulnerabilities, ensuring that our software stays in harmony with evolving data protection standards.
Transparent Privacy Practices: We supply transparent information about our data handling practices. Our privacy policy lucidly elucidates how we collect, process, and store data, offering your clientele the assurance they require.
Dedicated Support: Our support team is well-versed in data protection regulations. Should you possess queries or concerns regarding compliance, our experts are poised to assist you at every juncture.